 CryptPeer®
CryptPeer®
« The server sees without knowing »

Canonical definition
CryptPeer® is a sovereign end-to-end encrypted secure communication system, with no trusted third party, under the exclusive control of the licensee.
- No third party holds or exploits the keys.
- No data is accessible to a publisher.
- No post-deployment access is possible.
- Governance rests exclusively with the licensee.
Sovereign architecture
Sovereignty by Design / Licensee Exclusivity
- Each bubble (CryptPeer instance) is autonomous and isolated.
- No single point of centralized failure.
- Operates via standard HTTPS, with no trust transfer.
- The server transports, without ever knowing.
Technical note: Internet connection required only for HTTPS certificate validation (Let's Encrypt), DNS resolution of the licensee's domain, and browser compatibility. These exchanges introduce no external cryptographic authority.
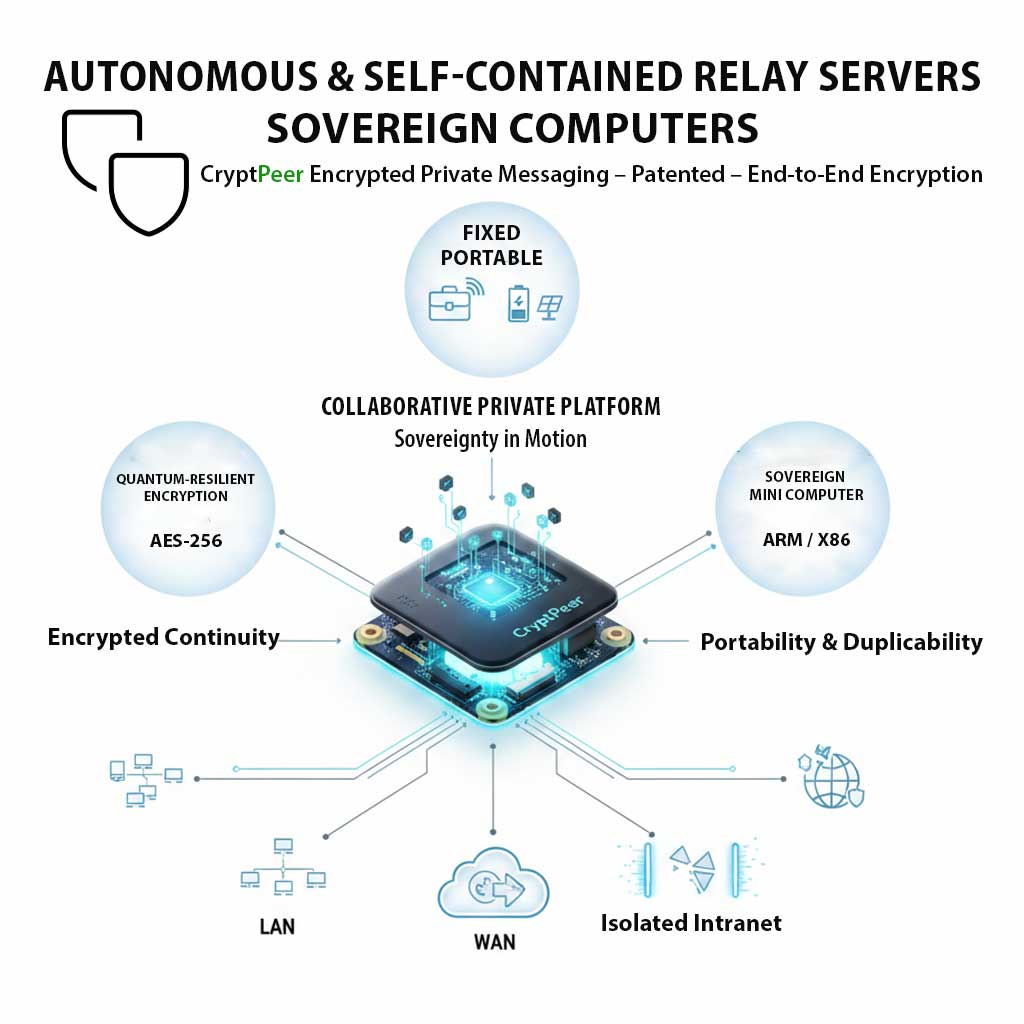
Available versions
| Version | Usage | Features |
|---|---|---|
| Standard | Professional communication | Full self-hosting |
| Nomad | Portable / offline use | Works on closed network |
| Site | Institutional deployment | Multi-bubble, internal governance |
All versions use the same cryptographic engine and respect the same sovereignty doctrine.
14 reasons to choose CryptPeer®
Proven, measurable and verifiable sovereignty.
Absolute sovereignty — No trusted third party, exclusive licensee control.
« The server sees without knowing » — End-to-end encryption + deterministic derivation.
ROI +200 % over 36 months — Proven gains over 3 years, operational autonomy.
TCO −62 % over 3 years — Licence + local hosting included.
Universal interoperability — 60+ browsers, 0 installation.
Multilingual sovereign assistance — 50+ languages, dedicated Translator tool, voice recognition (Android/Apple), file import (.txt, .docx, .pdf…) with embedded OCR. Messaging and e‑mail.
MFT included — Signed large file transfer included, savings €800–1,000/year vs dedicated solutions.
1-click test — test.cryptpeer.com/login
Quantum resilience by design — robust symmetric primitives (AES-256, SHA-3) and hardening.
Air-gap mode — Works on closed network.
Network resilience — Autonomous bubbles, no single point of failure.
Zero plaintext data — No key or metadata in plaintext.
Admin without cleartext access — Encryption on terminals, super admin for account deletion.
Dual-Use doctrine — Civil, institutional, defence — defensive only.
Regulatory compliance — GDPR, NIS2, DORA, CRA, dual-use regulation (EU 2021/821). Architecture designed for European standards.
Economic performance
Measurable ROI, reduced TCO
- ROI over 36 months: +170 to +200 %
- TCO over 3 years / user: −62 %
- 3-year TCO: Standard ≈€700 — Nomad ≈€1,000
Scope: licence + hosting + maintenance. Benchmark: messaging + file transfer.
Technologies and security
Total cryptographic sovereignty.
- AES-256-GCM — symmetric encryption
- PBKDF2-SHA-256 — local key derivation
- Segmented authentication (international patent WO2018154258)
- SHA-3 — “quantum-informed” hardening / hybrid derivation (symmetric)
- 2FA TOTP — Compatible with all TOTP key management software, including PassCypher HSM PGP and PassCypher NFC HSM (SHA1, SHA256, SHA512)
- No master key — no delegation
- Full encrypted storage (files and messages)
HTTPS protects transport — CryptPeer protects content.
Regulatory compliance
Designed to meet European and international framework requirements.
- GDPR / RGPD — Data minimization, privacy by design, E2E encryption, exclusive licensee control.
- NIS2 — Self-hosting, infrastructure control, no cloud dependency for communications.
- DORA — Operational resilience (financial sector): infrastructure under control, no critical third party.
- CRA — EU Declaration of Conformity (Cyber Resilience Act, Module A).
- NIST — Approved algorithms: AES-256 (FIPS 197), GCM (SP 800-38D), SHA-256, SHA3-512.
- ISO/IEC — Cryptographic standards (AES-256-GCM, PBKDF2, HKDF).
- LCPDP — Andorran data protection law (GDPR-aligned).
The licensee remains responsible for impact analysis and compliance according to their jurisdiction.
Network connectivity
CryptPeer operates on the Internet, but never through the Internet.
- DNS and domain belong to the licensee.
- Let's Encrypt only manages the TLS layer (no visible data).
- No external flow or metadata.
- Semi-connected mode possible: one-off HTTPS validation, then isolated operation.
Try CryptPeer®
No installation. No commitment.
Log in to test or sign up for production:
Partners
Access CryptPeer® through our partners:
Doctrinal statement
CryptPeer® is a defensive sovereign system, designed to protect communications, confidentiality and operational continuity. It provides no offensive, coercive or clandestine capability. Its use falls exclusively under applicable law and licensee responsibility.
 Test CryptPeer®
Test CryptPeer® Sign up (production)
Sign up (production) CryptPeer AMG PRO
CryptPeer AMG PRO CryptPeer Bleu Jour
CryptPeer Bleu Jour