The sovereign communication and collaboration platform, 100% self-hosted and under the licensee’s exclusive control.
CryptPeer is a sovereign digital infrastructure built on a patented segmented-key authentication system. The solution is physically self-hosted by the licensee, fully autonomous in operations, and designed with no external dependency. Messaging, calls, agenda, notes, translation, encrypted exchanges, secure email, and archiving are unified in one platform under full local control.
Why CryptPeer
Many organizations still stack fragmented tools for messaging, meetings, files, translation, notes, and email. CryptPeer provides a unified alternative: a sovereign, coherent, autonomous infrastructure physically controlled by the licensee. See the 15 reasons for the decision framework, and keep this page for platform vision and use-case overview.
- Messaging, video, files, email, and notes spread across multiple services.
- Sensitive flows exposed to multiple technical and contractual dependencies.
- Heavier administration and weaker governance consistency.
- Sovereignty often declared, but difficult to enforce in operations.
- One platform to communicate, share, translate, encrypt, and govern.
- Physical self-hosting by the licensee, with no cloud, no imposed third party, and no external dependency.
- Stronger control over flows, secrets, and lifecycle governance.
- Real sovereignty, continuously maintained under exclusive control.
Security and sovereignty by design
Security is not an add-on: it structures architecture, usage, secret management, and governance.
Zero external dependency
Full control of deployment and operations, with no cloud, no imposed third party, and no external dependency.
Better protected secrets
No-account third-party transfer with decryption secret unknown to the server and local decryption on recipient side.
Private key protection
In the encrypted email client, private keys remain password-protected and are decrypted only in volatile memory.
What the platform unifies in one experience
CryptPeer covers the full cycle of communication, collaboration, encrypted exchanges, and operational coordination. Technical glossary.
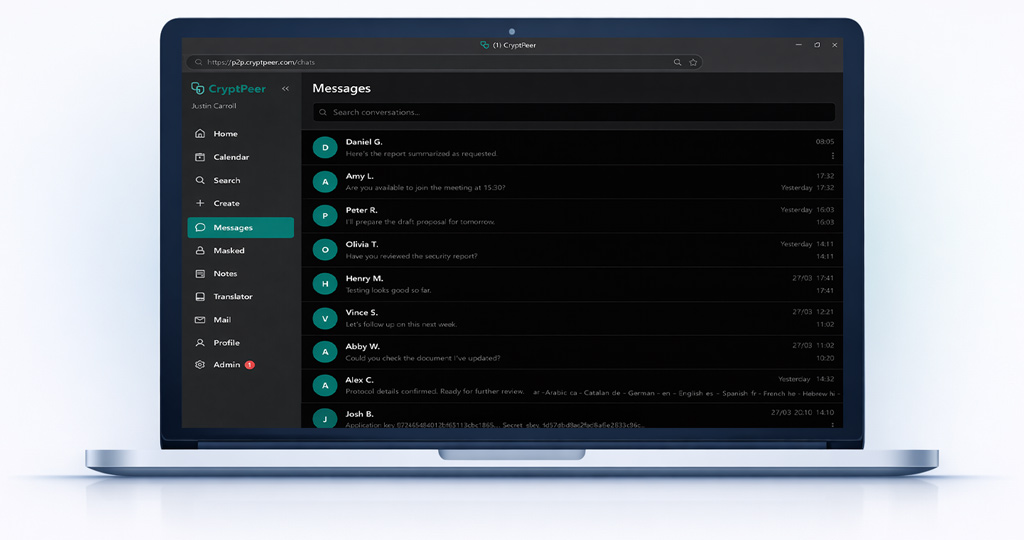
Secure messaging
Direct and group exchanges with protected content.
Audio and video calls
Integrated real-time communication without flow fragmentation.
Shared agenda
Team planning and event coordination.
Meeting polls
Create polls and synchronize outcomes with collective agenda.
Collaborative notes
Personal, shared, or co-edited notes in groups.
Embedded translation
Instant multilingual translation without imposed third-party service.
No-account third-party transfer
Send encrypted files to external recipients without account creation.
Encrypted multi-account email
Integrated email client with automated outbound encryption.
File encryption
Protect data before storage or distribution.
Inter-instance interoperability
Links between CryptPeer instances operated by different licensees.
Secure archiving
Encrypted exports and secure historical visualization.
Administration and governance
Centralized control, supervision, and operational policy framework.
Send encrypted files to third parties without accounts
CryptPeer covers secure transfer to external recipients, in direct competition with specialized services such as WeTransfer or SwissTransfer, with a sovereign zero-knowledge model. Secure transfer details.
Sender-side encryption
The user encrypts the file and defines retention before automatic deletion.
Controlled sharing
The download link and secret can be sent through separate channels.
Local decryption
The external recipient decrypts locally with the secret sent by the sender.
A foundation favorable to compliance
CryptPeer helps licensees address recurring requirements from frameworks such as GDPR, UK GDPR, NIS2, and other international standards related to data protection, cybersecurity, and accountability.
Data protection by design
Architecture designed to limit exposure and strengthen local control over access and sensitive flows.
Cybersecurity and risk management
Reduced dependency surface and stronger control of secrets in a sovereignty-first approach.
Simplified international compliance
Physical self-hosting, exclusive licensee control, and coherent local governance.
Test CryptPeer in real conditions
A dedicated test instance allows practical evaluation in a controlled context. View plans.
Access request
Request an account on the live test instance.
Validation and onboarding
Evaluate communication, sharing, coordination, and collaboration functions.
Controlled test lifecycle
Test accounts follow the lifecycle policy displayed on the instance.
Who it is for
For organizations that no longer want to trade off usability, high security, and real autonomy.
CIO, CISO, and cyber teams
Control sensitive communications, encrypted exchanges, and collaborative governance.
Public and industrial organizations
Deploy a coherent infrastructure in high-sovereignty, high-security environments.
Organizations in evaluation phase
Validate real use cases before wider autonomous rollout.
Move from intent to proof of use
Replace fragmented tool stacks with a sovereign, autonomous infrastructure physically controlled by the licensee.